How To Block Cell Phone Interception
Cloudwards.net may earn a small committee from some purchases fabricated through our site. However, whatever affiliate earnings do non bear on how we review services.
If surveillance is a topic y'all intendance about, you've probably heard the term "StingRay" thrown around in reference to law enforcement agencies tracking cell phones. In this commodity, we'll interruption downwardly exactly what a StingRay is, what it does and how to block StingRay surveillance using tools such as VPNs and network pick.
Although the term "StingRay" has become a scrap of a take hold of-all term, technically information technology merely refers to a single blazon of device. The more authentic umbrella terms for these kinds of devices is "IMSI catcher" or "cell-site simulator." IMSI is brusk for "international mobile subscriber identity, and it refers to the unique identifier attached to every SIM menu.
There are significant differences between actual StingRays and other, more avant-garde cell-site simulators, which we'll get into further down in this commodity.
Key Takeaways:
- StingRay devices are merely ane type of IMSI-catcher that targets legacy 2G or GSM networks by mimicking a cell belfry that your phone and so connects to.
- Protecting yourself against StingRays in particular means disabling 2G on a jailbroken device, living in an area with true 5G connectivity, or always using a VPN when connecting to mobile information.
- Many 5G networks are actually but 4G networks with upgraded speed, meaning it can exist difficult to tell if you're protected by 5G'due south security features or not.
- Currently, there is no legislation in the U.S. that limits the use of cell-site simulators for surveillance, but there is a pending bill that aims to require constabulary and other governmental agencies to obtain a warrant before deploying one.
If you'd rather but skip ahead to what you tin do to protect your online action, the short respond is to install and run a VPN at all times, so make certain to bank check out our list of the best VPNs to keep yourself safety. ExpressVPN (read our ExpressVPN review) and NordVPN (read our NordVPN review) are our clear favorites. Yet, annotation that VPNs won't protect your text letters.
-
Yep. Although a VPN won't stop your phone from performing the automatic handshake with the StingRay device, it volition garble any online information it picks up, making it unreadable to the person running the surveillance performance.
-
At that place are currently no laws prohibiting the apply of StingRay devices (or any other IMSI catcher, for that thing). Although their cost is prohibitive for individual individuals and hackers, police force and other regime agencies own many of them and are not required to obtain a search warrant to utilize them. That said, there is currently a bill that aims to require that local police departments and federal law enforcement acquire a search warrant before they can use such devices.
-
The best way to protect yourself from StingRay devices in particular is to jailbreak your phone and install software that lets you disable 2G connectivity. This still leaves yous open up to automated downgrades on 3G and 4G networks, though, so if you're worried about this type of surveillance, you lot'll want to run a VPN too. Connecting to a true 5G network as well protects your information as there are no known IMSI catchers for 5G networks.
-
Constabulary enforcement does non need an IMSI-catcher to runway the location information of a cell phone. Once a device connects to iii or more than regular jail cell towers (or if information technology runs GPS), police can utilize triangulation to pinpoint the location of the device.
How to Block Stingray Surveillance
We'll start out our guide past looking at what a StingRay is and how it differs from more modern solutions. Then we'll explicate the almost basic steps you tin can accept to protect yourself against StingRay surveillance.
What Is StingRay Surveillance?
StingRays essentially office by tricking your telephone into thinking that the surveillance device is a prison cell tower. This results in your telephone routing any traffic — such as text letters, web queries or phone calls — through the device. If this traffic isn't encrypted, whoever operates the StingRay device will be able to access all of it.
Although it's often used as a blanket term, a StingRay device is merely i type of a class of devices known as "IMSI catchers" or "cell-site simulators." Information technology only operates on 2G networks, which makes it less useful for law enforcement with every passing year equally 4G and somewhen 5G networks take over.
Because of this, StingRays aren't every bit useful every bit they used to be. Luckily for law enforcement and surveillance agencies, information technology's not the end of the line for this type of technology.
StingRay vs Hailstorm
Although StingRays are limited to tracking cell phone users connected over a legacy 2G network, the aforementioned company that produced the StingRay (the Harris Corporation) also manufactures a device known as Hailstorm (or just "StingRay Two").
Where StingRays tin only intercept data over 2G, a Hailstorm device operates on 3G and 4G networks, which make upwards the vast majority of cellular networks worldwide.
Unlike with StingRays and similar devices, protecting yourself against a Hailstorm assail is much more hard. Unless y'all alive in an area with true 5G networks (more on that later), your only adventure of keeping data similar SMS messages safe from Hailstorm devices is to always use a VPN.
Block StingRay by Disabling 2G
The virtually straightforward way to protect yourself against StingRay attacks is to disable 2G networking on your phone. Unfortunately, very few phone manufacturers permit you to practise this, with all of the big companies (such as Apple and Samsung) just letting you disable 3G or 4G.
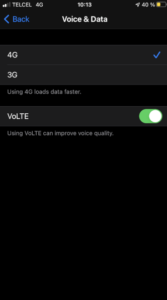
Very few modernistic smartphones will let you disable 2G entirely.
To get around this, y'all tin can jailbreak or root your phone and install third-political party software such every bit the Xposed Framework to disable 2G connections. That said, this just protects you if your phone connects directly to a 2G network, simply not against the security vulnerability in 3G and 4G cellular networks that automatically switches the point to 2G if needed.
What'due south worse is that the StingRay in itself is an outdated applied science. Police force enforcement agencies besides have access to more modernistic cell-site simulators that target 3G and 4G networks, making them much harder to avert entirely.
In fact, U.S. carriers are in the procedure of phasing out their 2G networks. AT&T stopped servicing their 2G network in 2017 and Verizon did in 2020. Dart and T-Mobile aren't quite as far along, but they also program to phase out their 2G networks by December 2021 and December 2022, respectively.
Can VPNs Protect You From Other Cell-Site Simulators?
Partially, yes. Although a virtual individual network will garble any data or traffic that's picked up by IMSI catchers, such every bit a StingRay device, it won't be able to hibernate your physical location (or, at least, that of your device).
Standard text messages likewise won't be protected, and then make sure you use an alternative messaging app like WhatsApp, Signal or fifty-fifty Facebook Messenger if yous desire your messages covered by the VPN.
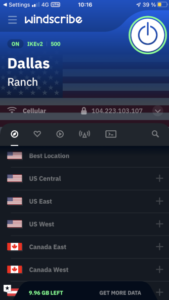
Using a VPN when yous're on mobile data will proceed the contents of your network traffic safe from anyone listening in with an IMSI catcher.
That said, protecting the contents of your information is probably more important than the fact that your device was located somewhere, unless you're currently evading a manhunt. Besides, police force enforcement doesn't even demand a prison cell-site simulator such as a StingRay if all they demand is your location, as this tin exist found out by triangulating regular cell-telephone towers or your GPS betoken.
Who Uses Cell-Site Simulators?
Prison cell-site simulators are in wide utilise beyond the U.S., U.Thousand. and Canada. They're primarily used by government agencies, simply in theory, there's nil stopping random cybercriminals from deploying one.
Law Enforcement Agencies
The chief usage of cell-site simulators comes from law enforcement. Although y'all might think that using these devices requires a warrant, much like borer someone's phone, that is non the case. Cell-site simulators have long existed in a sort of legal gray area, which has allowed law to use them indiscriminately.
That said, a bill has been introduced in the United States Congress that would crave police enforcement to obtain a warrant before deploying such a device, just whether or not it becomes law remains to be seen.
Intelligence Agencies
Given the murky legal nature of prison cell-site simulators, it'due south not surprising that they're widely used by intelligence agencies such as the NSA or CIA.
The relative lack of oversight these types of organizations bask makes information technology difficult to determine exactly how widespread this type of surveillance is. The American Civil Liberties Union found 75 different agencies — including the FBI, DEA and NSA — brand use of this type of surveillance.
Hackers
Although there's nothing stopping hackers and cybercriminals from using cell-site simulators to access people's data, their toll and the need to be in physical proximity to the target device make them much less bonny than other types of attacks for any but the nigh focused and dedicated cybercrime operations.
5G Networks: A Solution?
The solution to all of this is truthful 5G. As opposed to 3G and 4G networks, 5G does not automatically reroute traffic through 2G without you knowing it. As of yet, there are no known IMSI catchers that can pick upwardly 5G traffic, though it wouldn't surprise u.s.a. if this changes once 5G networks become more widespread.

True 5G networks fix the security vulnerabilities used by StingRay technology to obtain information from nearby devices.
The reason 5G networks are safer from surveillance by law enforcement officials is that they ditch the IMSI — which is unencrypted and permanent — for the encrypted SUPI (subscription permanent identifier) and the unencrypted SUCI (subscription concealed identifier), which can't be used to identify y'all considering it's reset with each connectedness.
That said, 5G networks are still relatively rare, and then we wouldn't be surprised if a "SUPI catcher" is already in the works somewhere.
Real & "Fake" 5G Networks
Since 5G networks don't have the same security vulnerabilities as 4G, you might remember you're safe from surveillance in one case y'all see that you're continued to a 5G network. Unfortunately, nigh 5G networks are even so actually just 4G, simply with upgraded speed and bandwidth.
This means that even though it looks like you're connected to 5G on your device, the underlying technology is nevertheless 4G, which leaves you vulnerable to Hailstorm devices.
Unfortunately, you every bit the end user won't really be able to tell whether the 5G network y'all're connecting to is truthful 5G or simply upgraded 4G. The simply option yous have for finding out is to contact your telephone carrier and ask them, but whether or non you'll become a truthful answer depends on the company.
Concluding Thoughts: Blocking StingRay Technology
That'southward the end of our guide on how to protect yourself from surveillance carried out with StingRays and similar devices. Although there is legislation awaiting to limit the use of these devices, it'south currently a complete free-for-all, which means that it's up to you lot to take steps to protect yourself.
At the end of the solar day, the best way to ensure you're protected is by using a VPN for whatever mobile data network you connect to. Another safety measure you tin implement is to ditch traditional SMS letters in favor of encrypted messages with an app similar Signal, Telegram or Wickr.
What did you recollect of our guide to cellular surveillance? Exercise you feel similar yous have a better understanding of how federal law enforcement, intelligence agencies and police departments monitor mobile devices? Is there some crucial detail yous think we missed? Let us know in the comments below. Cheers for reading.
How To Block Cell Phone Interception,
Source: https://www.cloudwards.net/how-to-block-stingray-surveillance/
Posted by: loefflergivy1941.blogspot.com


0 Response to "How To Block Cell Phone Interception"
Post a Comment